A joint cybersecurity advisory from the Federal Bureau of Investigation, Cybersecurity and Infrastructure Safety Company, Division of Well being and Human companies and Multi-State Data Sharing and Evaluation Middle was lately launched to offer extra details about the Black Basta ransomware.
Black Basta associates have focused organizations within the U.S., Canada, Japan, U.Ok., Australia and New Zealand. As of Might 2024, these associates have impacted greater than 500 organizations globally and stolen information from a minimum of 12 out of 16 essential infrastructure sectors, in accordance with the joint advisory.
Latest safety analysis signifies ransomware threats are nonetheless excessive, and extra firms are paying the ransom calls for to get better their information.
What’s Black Basta?
Black Basta is ransomware-as-a-service whose first variants have been found in April 2022. In accordance with cybersecurity firm SentinelOne, Black Basta is very doubtless tied to FIN7, a menace actor often known as “Carbanak,” energetic since 2012 and affiliated with a number of ransomware operations.
Rumors have additionally unfold that Black Basta may need emerged from the older Conti ransomware construction, but cybersecurity firm Kaspersky analyzed each code and located no overlap. The rumors are principally primarily based on similarities within the modus operandi of Conti and Black Basta, but with out strong proof.
How do Black Basta associates function?
Black Basta associates use frequent methods to compromise their goal’s community: phishing, exploitation of recognized vulnerabilities or the acquisition of legitimate credentials from Preliminary Entry Brokers. Black Basta was deployed on techniques by way of the notorious QakBot.
As soon as contained in the community, the associates use a wide range of instruments to maneuver laterally via the focused community to steal delicate content material after which deploy the ransomware (double-extortion mannequin). Widespread administration or penetration testing instruments — resembling Cobalt Strike, Mimikatz, PsExec or SoftPerfect, to call a couple of — are used to realize this activity.
A variant of Black Basta additionally targets Linux-based VMware ESXi digital machines. The variant encrypts all of the recordsdata within the /vmfs/volumes folder that shops all of the recordsdata for ESXi’s digital machines, leaving a ransom notice after the encryption.
As soon as the ransomware has been deployed, a ransom notice is unfold on the techniques. The ransom notice incorporates a singular identifier the group must contact the cybercriminal by way of a Tor hyperlink.
A countdown begins on the Black Basta Tor web site, exposing firm names and details about the information Black Basta owns. As soon as the timer will get to zero, the stolen information is being shared.
Should-read safety protection
The state of ransomware: Key traits, together with ransom funds
Black Basta ranked the twelfth most energetic household of 2023
In accordance with Kaspersky in its newest findings in regards to the state of ransomware in 2024, Black Basta is ranked the twelfth most energetic ransomware household in 2023, with a 71% rise within the variety of victims in 2023 as in comparison with 2022.
Kaspersky’s incident response crew stories that each third safety incident in 2023 was associated to ransomware.
SEE: In 2022, Black Basta was thought-about one of the vital harmful and harmful ransomware teams
As well as, the researchers famous one other necessary pattern noticed in 2023: Assaults by way of contractors and repair suppliers, together with IT companies, turned one of many prime three assault vectors for the primary time. These sorts of assaults permit cybercriminals to spend much less effort on the preliminary compromise and lateral actions and infrequently keep undetected till encryption of the techniques is completed.
Extra organizations paid the ransom in 2023
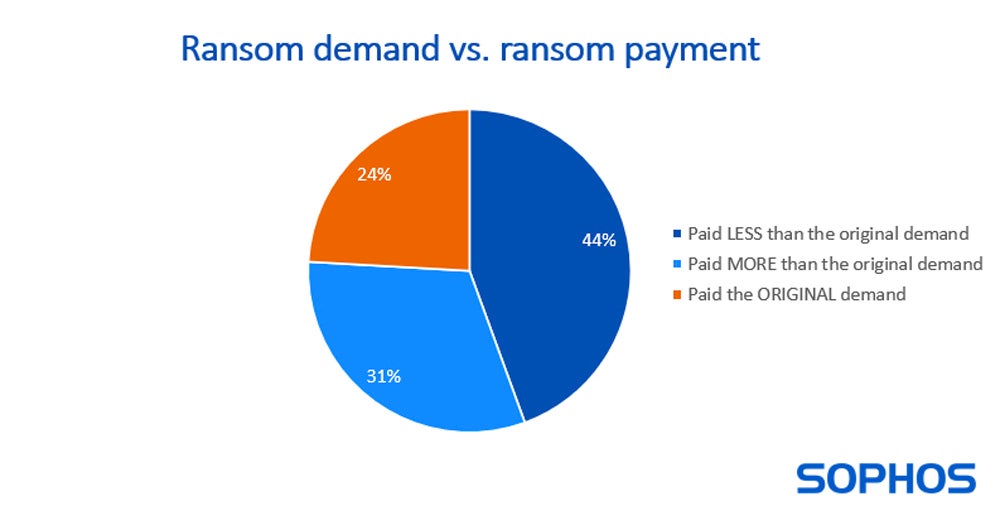
Cybersecurity firm Sophos in its yearly state of ransomware survey famous that, for the primary time, greater than half (56%) of the organizations that had fallen to ransomware admitted they paid the ransom to get better their information in 2023.
For the organizations that determined to pay, 44% paid lower than the unique ransom quantity, whereas 31% paid extra.
The way to mitigate this Black Basta ransomware menace
Suggestions from CISA to all essential infrastructure organizations are the next:
Updates for working techniques, software program and firmware ought to be put in as quickly as they’re launched.
Phishing-resistant multifactor authentication have to be required for as many companies as potential.
Consciousness ought to be raised; customers ought to be educated to acknowledge and report phishing makes an attempt.
Distant entry software program have to be secured and monitored. Specifically, community directors and defenders should have the ability to acknowledge irregular conduct and detect malicious use of these software program.
Zero-trust options have to be used when potential. The precept of the least-privilege use ought to be utilized when not potential.
Inactive or out of date accounts within the Lively Listing ought to be audited.
Safeguards for mass scripting have to be used, along with a script approval course of. An account making an attempt to push instructions on a number of units inside a sure time frame ought to see its safety protocols being retriggered, resembling MFA, to make sure the supply is professional.
Backups of essential techniques and system configuration have to be performed continuously to allow units to be repaired and restored.
Trendy antimalware software program have to be used, with computerized updates of the signatures the place potential.
Exercising, testing and validating the group’s safety program in opposition to menace behaviors mapped to the MITRE ATT&CK for Enterprise framework within the joint advisory is very really helpful.
Extra mitigation methods can be found within the #StopRansomware Information from CISA.
Disclosure: I work for Development Micro, however the views expressed on this article are mine.



















/cdn.vox-cdn.com/uploads/chorus_asset/file/25601626/ad3527b123d0c8dfcca5d4968a6dcf126e37a68dd290ef85.jpg?w=120&resize=120,86&ssl=1)
