Most defenders are acquainted with tips on how to discover and search for suspicious RDP lateral motion, whether or not which means wanting based mostly on known-compromised customers or on an alert from antimalware or EDR protections related to a particular person. You’re beginning to pivot from the preliminary discover that one thing’s incorrect; now what?
Inspecting the logs to test account-activity timestamps is a typical method to spot odd conduct – for instance, James-from-the-head-office connecting to a website controller at 3 a.m., when he usually solely accesses the Sage servers, and people solely throughout enterprise hours. Nonetheless, there’s extra to learn about logins – not simply when the exercise occurred, however the time zone from which the exercise originated. This is named the bias, and it’s captured on trendy (Home windows 10 / Server 2016 and later) variations of Microsoft’s working system. Occasion ID 104 is on the market within the Microsoft Home windows Distant Desktop Companies RDP Core TS Operational occasion log.
What does the defender see?
As one may count on from the title, this occasion logs the time-zone bias from UTC of the machine making the connection. Because you in all probability already know the time zone(s) your customers would usually be logging in from, seeing deviations from that zone may help you determine suspicious RDP connections, just because they’re not coming from the a part of the planet they need to be.
Taking James as our instance once more, let’s say James is predicated in London and that you simply’re investigating suspicious exercise within the early months of the 12 months. In January or February, the time-zone bias for James could be zero hours UTC, so if James is utilizing RDP to hook up with the community for no matter purpose, the consumer time bias you must see on his logins is [0]. If, immediately, you begin seeing consumer time zone biases of [-8], or [6], or different values that differ from the norm for James, that might allow you to spot probably suspicious RDP connections, or at minimal extra questions price asking. (Is he touring? Was his machine stolen?)
Let’s take an instance the place a person’s credentials have been phished, the attacker’s logged into the VPN — since you don’t have MFA enabled, although you understand you must — and so they begin accessing gadgets utilizing RDP. You’ll then begin to see the time zone of that attacker machine for these entry occasions.
There’s no single question that magically delivers each reply, and this one’s no exception. As an example, attackers typically host their machines hosted on varied machines, positioned in varied time zones by which they might or is probably not bodily positioned. Nonetheless, they’re more likely to differ from the traditional time zones for your customers.
One other potential weak point lies in false positives; in case your group operates in a method that makes it arduous to discern what a “regular” time zone appears to be like like, it might be tougher so that you can pinpoint the distinction between sign and noise. Lastly, false negatives are a risk; the occasion information the time zone on the attacker’s machine, so the attacker can undermine this information by altering the time zone on that machine. That mentioned, Occasion 104 is a useful occasion to maintain watch over – another device in your protection toolkit.
Timezone bias and Dwell Uncover
Occasion 104 is in fact obtainable to anybody inspecting Microsoft methods of the supported vintages (once more, Home windows 10 / Server 2016 and later). The knowledge within the ultimate part of this put up is offered for these readers utilizing Sophos’ Dwell Uncover to get the job finished. (Nonetheless, we’ll publish the question we’re about to debate on our Github, the place anybody can choose up a duplicate.) We additionally display this question and its outcomes on our YouTube channel.
To execute an OS question and return timezone bias info in Dwell Uncover, use the next:
SELECT
strftime(‘%Y-%m-%dTpercentH:%M:%SZ’,datetime) AS Datetime,
supply,
eventid,
JSON_EXTRACT(information, ‘$.EventData.TimezoneBiasHour’) AS TimezoneBiasHour
FROM sophos_windows_events
WHERE
supply=”Microsoft-Home windows-RemoteDesktopServices-RdpCoreTS/Operational”
AND eventid IN (104)
The output of the question appears to be like just like the outcomes proven in Determine 1:
Determine 1: Both the person has found a method to teleport themself and their pc throughout eight time zones in 90 seconds, or one thing is incorrect right here
On the left within the picture above, we’ve got the endpoint title – the identical for each entries on this two-event log. We see the date/time info in UTC, which reveals that the 2 occasions occurred a few minute and a half aside. The supply is the place we discovered this occasion, which is proven as 104 within the subsequent column. And on the appropriate, we see the outcome – the primary occasion originating in UTC 0, the second UTC +8, which is the realm indicated within the map in Determine 2.
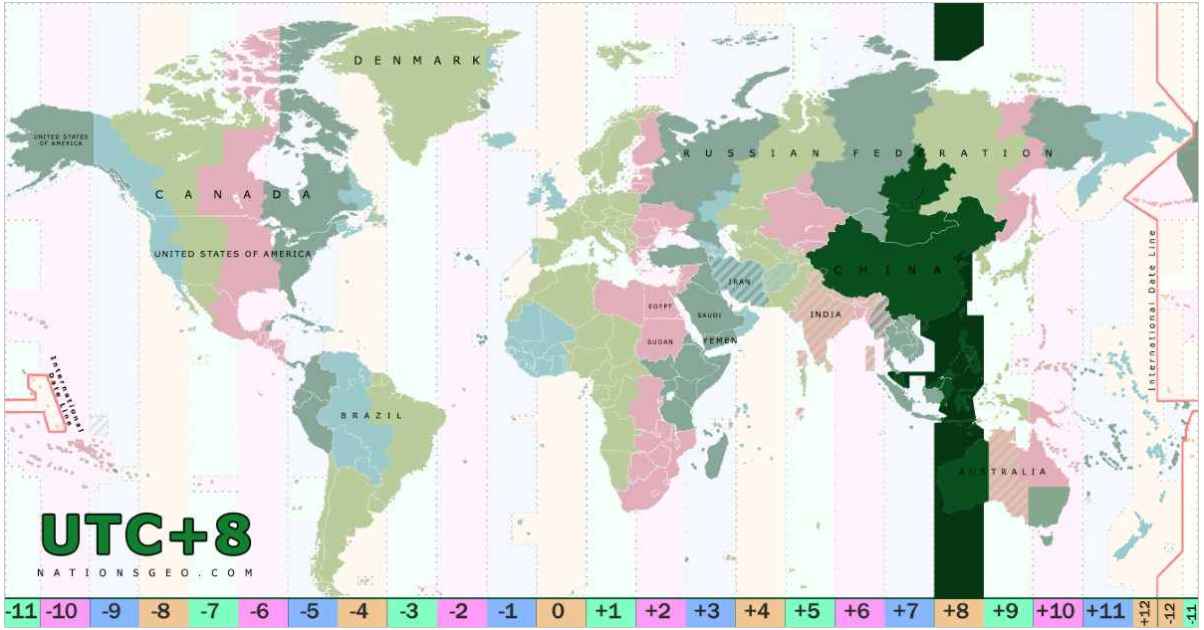
Determine 2: UTC +8 is a captivating slice of the planet, nevertheless it’s positively not close to James in London. (Map picture courtesy nationsgeo.com)
We suggest executing this question throughout all gadgets inside your setting – go searching and determine if there are timezone bias entries within the RDP Core TS Operational occasion log that differ from what you’d usually count on.
Distant Desktop Protocol: The Sequence
Half 1: Distant Desktop Protocol: Introduction (put up, video)Half 2: Distant Desktop Protocol: Uncovered RDP (is harmful) (put up, video)Half 3: RDP: Queries for Investigation (put up, video)Half 4: RDP Time Zone Bias ([you are here], video)Half 5: Executing the Exterior RDP Question (put up, video)Half 6: Executing the 4624_4625 Login Question (put up, video)GitHub question repository: SophosRapidResponse/OSQueryTranscript repository: sophoslabs/video-transcriptsYouTube playlist: Distant Desktop Protocol: The Sequence





_dennizn_alamy_2.jpg?disable=upscale&width=1200&height=630&fit=crop&w=350&resize=350,250&ssl=1)














